
Five Questions Every CISO Must Ask to Strengthen Ransomware Resilience
Ransomware has evolved beyond disruption
Ransomware has evolved beyond disruption; It now threatens business survival. Malware creates exposure, but once ransomware encrypts your data, the real risk is losing the ability to recover.
Picture the boardroom: a director leans forward and asks the CISO a simple question:
If ransomware hits tonight, can you prove we’ll recover without compromise?
The room goes quiet. In that moment, the CISO realizes prevention is expected—but proof of recovery is what truly matters.This is the existential challenge every enterprise faces today: guaranteeing recovery that is provable, uncompromised, and fast enough to keep the business running.
Here are five questions every CISO must ask going into Q4 or 2026:
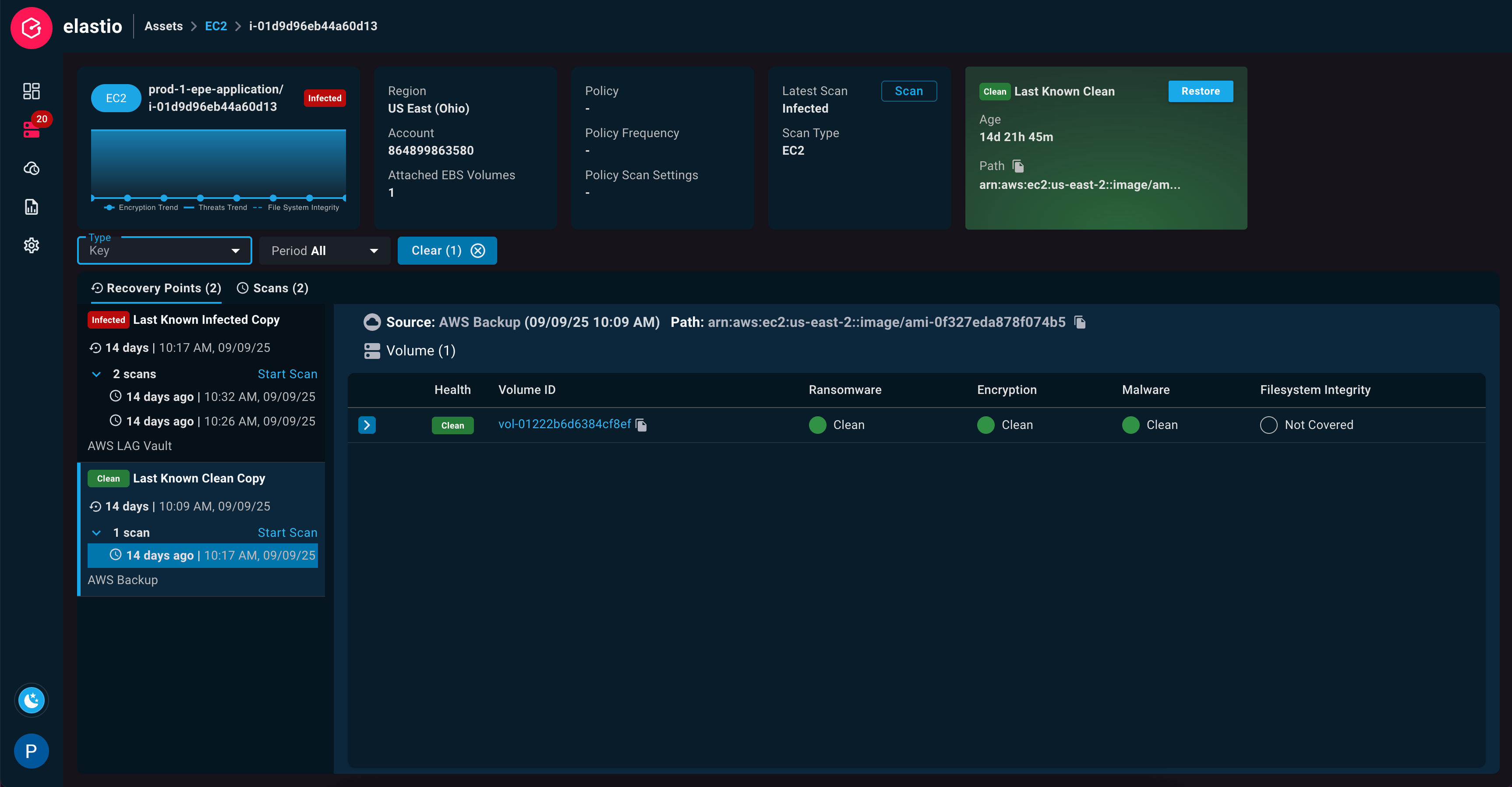
1. Can we prove that your backups are free of ransomware?
Backups that contain hidden encryption or dormant malware are liabilities, not assets. Without continuous validation of backup integrity, recovery risks reintroduce ransomware into production.
Boards should press for evidence-based assurance that every backup is verified, uncompromised, and ready to support recovery. Anything less is not resilience—it’s roulette.
2. How quickly can we identify a clean recovery point?
Downtime costs escalate minute by minute. Manual validation is too slow, and attackers know it.
An AI-driven recovery platform can accelerate the detection of clean recovery points, enabling day-zero recovery. Speed to recovery is no longer just a technical metric—it is a competitive advantage that protects revenue, brand, and customer trust.
3. Are recovery processes embedded into our workflows?
Recovery cannot sit on the sidelines. It must be built into daily operations—integrated with security tools, cloud platforms, and incident response.
When recovery is operationalized, it reduces risk, eliminates human error, and ensures resilience is invisible but indispensable.
4. Do we have provable evidence of clean recovery?
Boards, regulators, and customers no longer accept verbal assurances. They expect audit-ready proof that recovery is uncompromised.
Recovery is not just a technical function—it is a fiduciary responsibility. CISOs and executive leadership must be able to show verifiable resilience to those who hold them accountable.
5. Are we ready for AI-driven decision-making?
As AI systems increasingly automate critical workflows, resilience must become autonomous and self-healing.
Future-ready organizations will rely on AI to detect, validate, and recover—without manual intervention. But those systems can only be trusted if they operate on clean, uncompromised data.
Final Thoughts: Closing the Missing Control
Traditional security and immutable backups are no longer enough. The missing control is data integrity verification—the assurance that every recovery point is clean and trustworthy. Without it, cyber resilience remains a gamble.
Elastio closes that gap. By validating backups, detecting ransomware at day zero, and delivering provable recovery assurance, we enable CISOs to demonstrate resilience with confidence—to boards, regulators, and customers alike.
CISOs who can prove recovery don’t just mitigate ransomware risk. They redefine resilience as a board-level business advantage—the difference between disruption and survival.
Whether you're a CISO, IT lead, or cyber champion, this piece offers strategic insights to rethink your cybersecurity posture. Ready to explore how Elastio can fortify your defense-in-depth strategy—and why it’s emerging as a must-have for ransomware readiness? Let’s dive in.
Learn More at www.elastio.com/platform
Download
Can you prove your recovery points are clean?
Your board will ask if you can recover clean. This checklist lets you answer with evidence.
