
Responding to a Ransomware Attack: Clean Recovery Options are Critical
Ransomware attacks are a numbers game involving a constant barrage of attempts until one inevitably breaches the defenses. It is critical to have a robust
Recover in minutes -not months
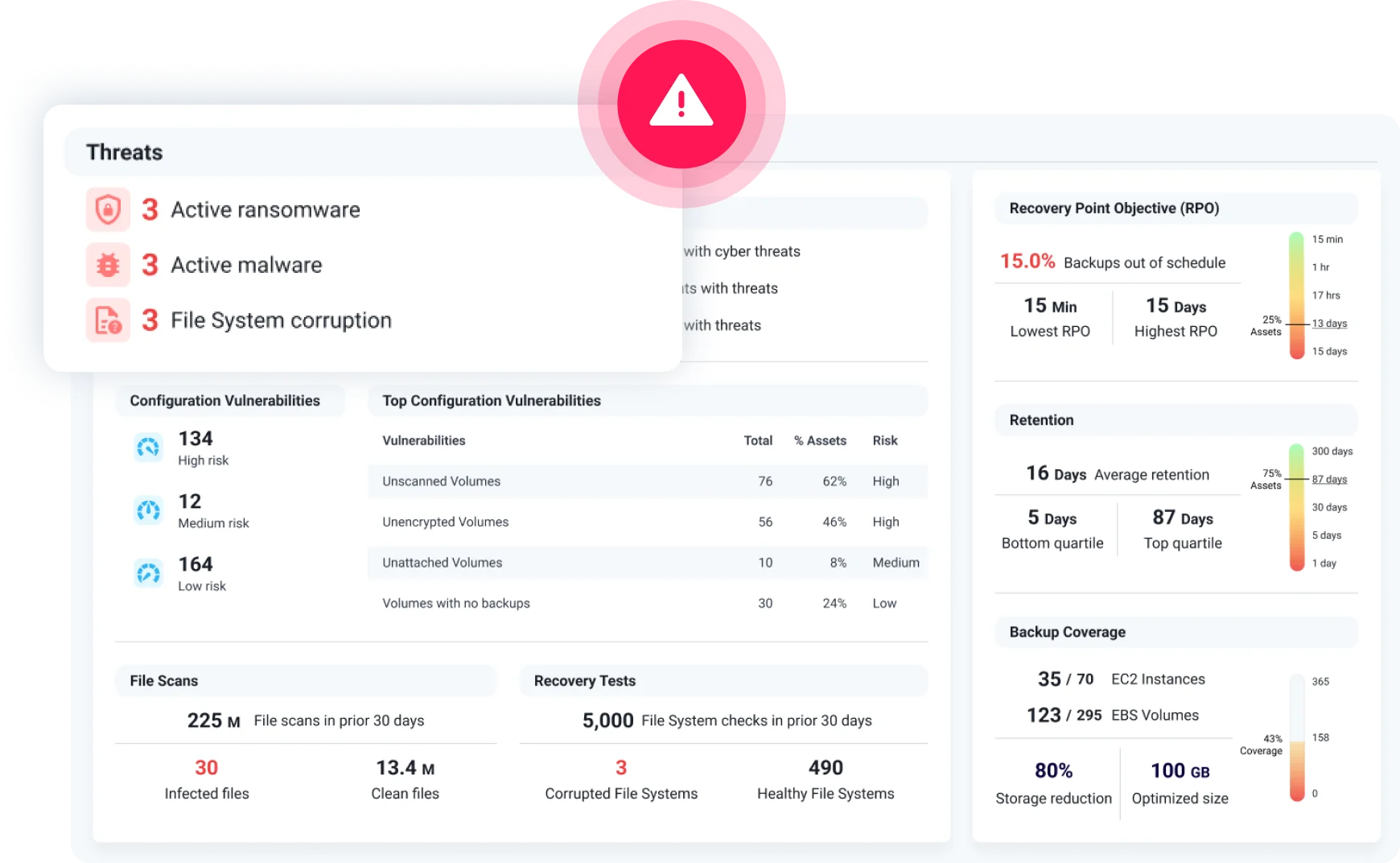
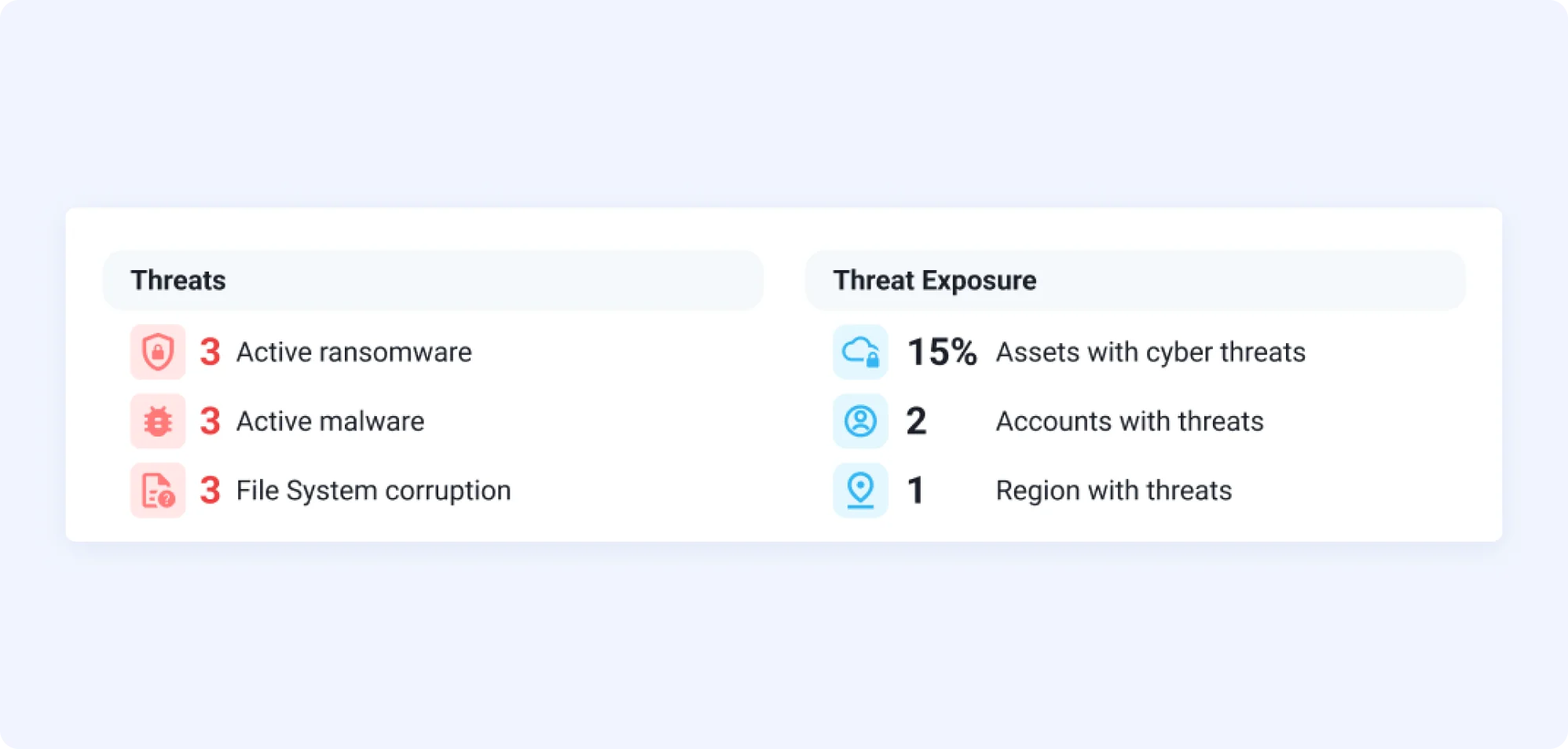
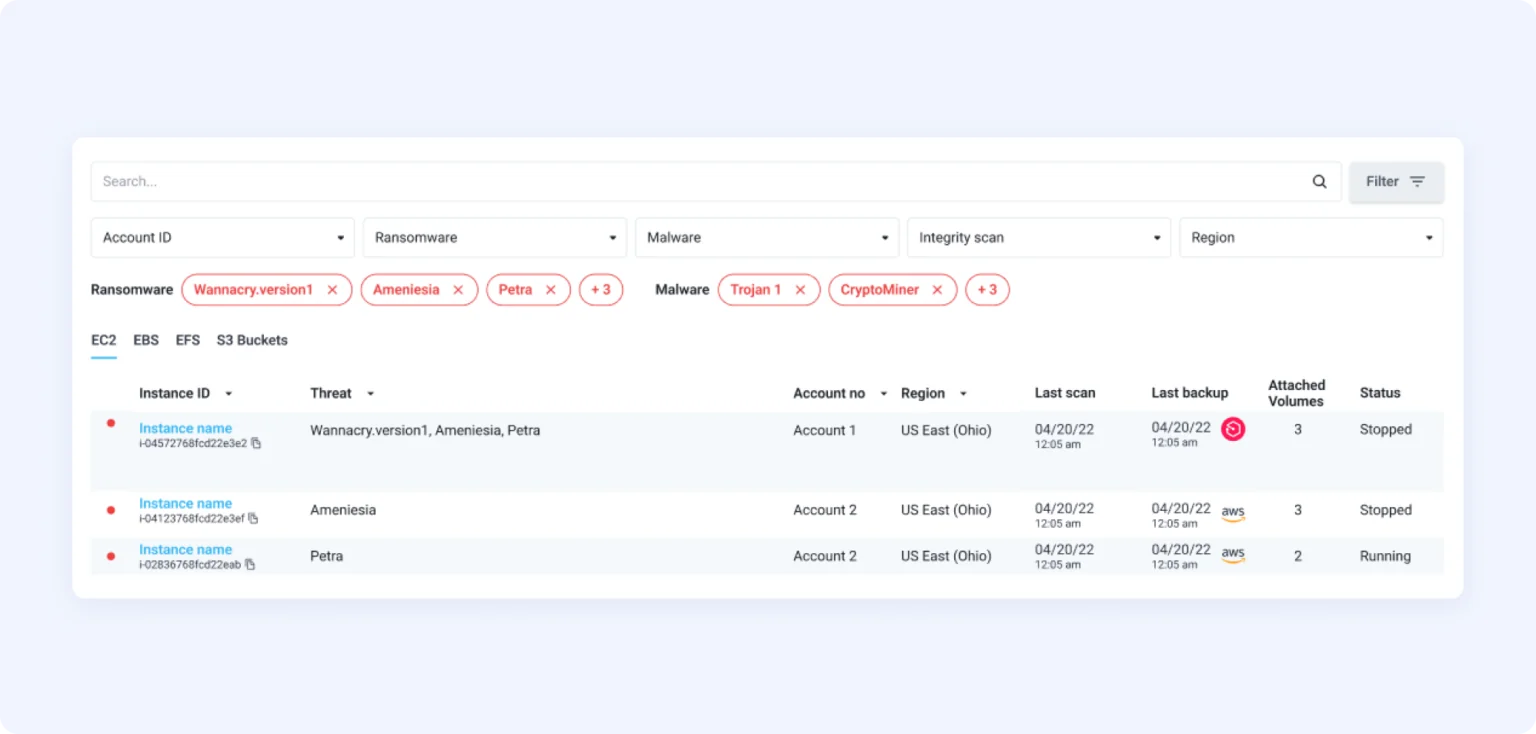
When existing cloud security measures fail to protect against cyber-attacks, Elastio detects and precisely identifies ransomware in the data and assures rapid post-attack recovery.
“We are excited to tell our customers we have the Elastio level of protection. It helps us land and keep more customers as we expose what we do with their data to them.
– TJ Schoessow, SVP of Technology & Business Systems, Caret


Elastio’s agentless platform never moves your data from your network.

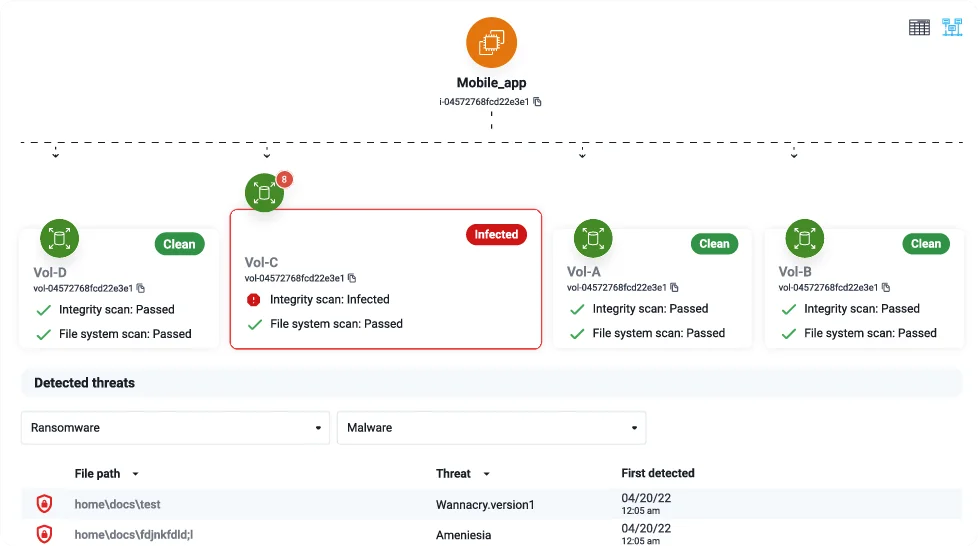
The world’s most comprehensive library of 2200+ ransomware families built on Machine Learning for accurate detection.

Elastio’s incident response team investigates alerts, avoiding alert fatigue.

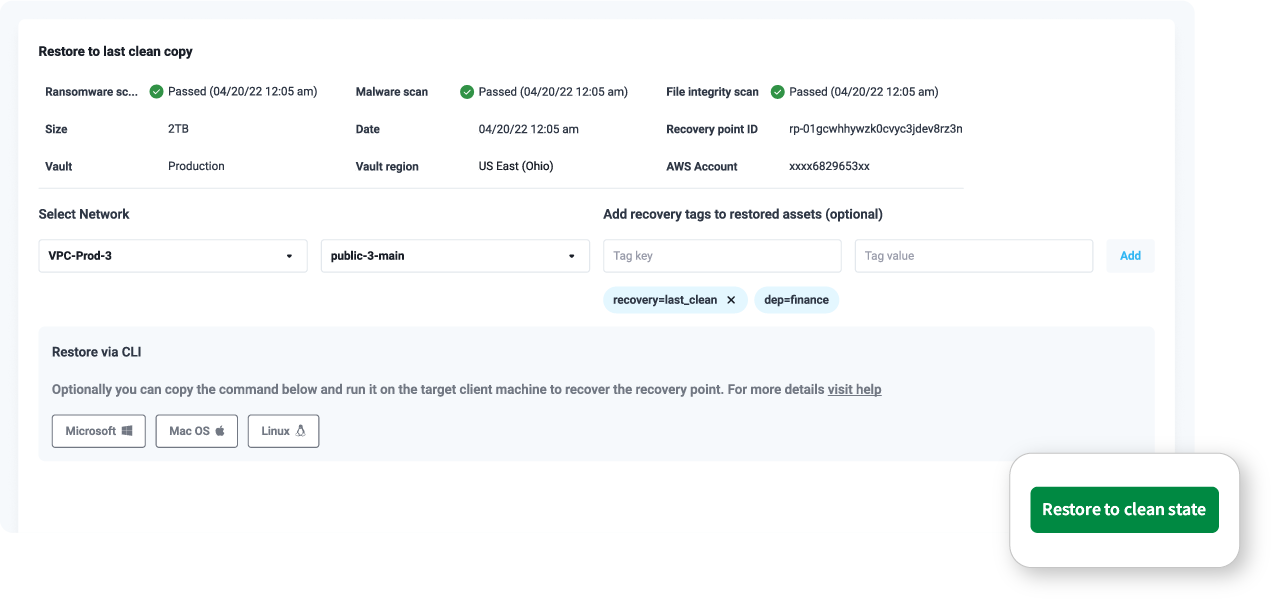
Point-in-time restoration of applications and data to a known clean copy.











How It Works
Case Study
“We are excited to tell our customers to have the Elastio level of protection… Our customers were sending over many gigs of data and we were finding malware in the customer data sets. That was an aha moment for us.”
– TJ Schoessow, SVP of Technology & Business Systems, Caret
Case Study
“As the application scales, Elastio automatically detects the new persistent volumes, inspects them for ransomware, and creates a recovery point. This ensures we always have a safe recovery option for our customer environments.”
– Greg Aligiannis, CISO, IBM
Case Study
“Elastio gives us data security and cyber recoveries in one platform, streamlining operations and improving business continuity.”
– Tricia Remacle, Chief Technology Officer, LeaseAccelerator

Ransomware attacks are a numbers game involving a constant barrage of attempts until one inevitably breaches the defenses. It is critical to have a robust

Learn to protect EKS clusters from evolving ransomware threats, ensuring operational continuity and safeguarding their data.

Learn to protect EKS clusters from evolving ransomware threats, ensuring operational continuity and safeguarding their data.